Image: nitpicker / Shutterstock.com
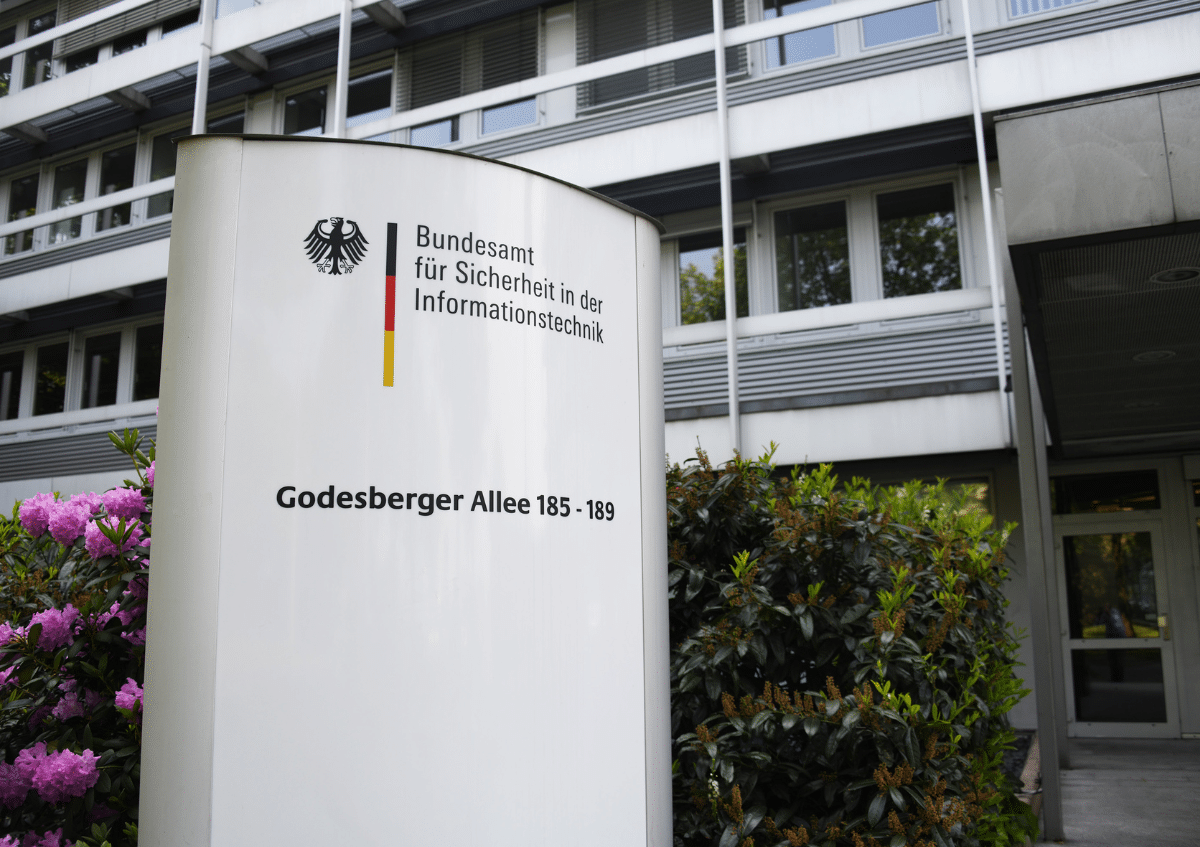
It sounds like a bureaucratic detail. But it isn't. Around 29,000 companies in Germany must register with the Federal Office for Information Security (BSI) by March 6, 2026. Those who fail to act now risk more than just a fine. It's a matter of responsibility, liability—and, in serious cases, the future of their own business. Heise Online reports with reference to TÜV SÜD.
The NIS2 regulation has been in force since December 6, 2025, and requires companies in sensitive sectors to implement clear security measures. Energy, health, transportation, digital infrastructure, and public administration—the government is now taking a closer look at all areas where a failure would have massive consequences. Companies with 50 or more employees or with annual revenues of more than €10 million are affected.
Registration is not a mere formality
Many companies still feel secure. But that is precisely where the problem lies. "Many companies underestimate the importance of formal obligations such as registration, ongoing updating of company data, and timely reporting of security incidents," warns Richard Skalt, Advocacy Manager Cybersecurity Office at TÜV SÜD.
Registration is done via a new online portal set up by the BSI. This is the central point of contact for everything related to NIS2. Among other things, companies must specify their size, legal form, the contact person responsible for NIS2, the sector concerned, and the responsible supervisory authority. And it's not a one-time entry: any changes must be reported within two weeks.
The portal also serves to report security incidents. Additional functions have been announced, including a standardized reporting format and rapid exchange of threat data. The goal is to detect attacks more quickly and respond to them jointly.
Nothing works without ELSTER
What surprises many people even more is that an ELSTER organization certificate is required for registration. And that doesn't happen overnight. According to TÜV SÜD, processing takes five to ten business days. So anyone who waits until shortly before March 6 to take action could fail to meet this requirement alone.
This shows how seriously the issue is being taken. It is not simply a matter of a mandatory online form. It is about mandatory integration into a government security system.
Managing directors have a duty
Another point is particularly controversial: responsibility does not end with the company as a legal entity. Managing directors can be held personally liable if they fail to implement the requirements appropriately. So anyone who has previously delegated IT security to the IT department should take a closer look now, if they haven't already.
Skalt sums it up: "Organizations need practical, actionable plans for NIS 2." It's not enough to just put a paper concept in a drawer. What's needed are real processes, clear responsibilities, and emergency plans that work.
Between increased security and bureaucratic burden
Of course, the question arises: Is all this necessary? The threat situation in cyberspace is real. Attacks on hospitals, energy suppliers, or government agencies are no longer theoretical, but everyday occurrences. A successful attack can cost millions and, in the worst case, endanger human lives.
At the same time, NIS2 means considerable additional expense for many medium-sized companies. New processes, training, documentation requirements—all of this ties up resources. Smaller companies in particular, which are just above the thresholds, are feeling the strain significantly.
Our classification
The direction is right: anyone who offers critical services must also protect them. It is difficult to justify that central infrastructure depends on poorly secured IT systems. The personal responsibility of management ensures that the issue is no longer put on the back burner.
However, implementation must not degenerate into a mere checklist exercise. If companies primarily fill out forms instead of establishing genuine security structures, the objective will be missed. Security is not created by portals, but by putting practices into action.
The decisive factor will be whether the BSI provides pragmatic support or merely exercises control. Pressure alone does not create resilience. Anyone who is only focused on the deadline is thinking too short-term. The real work begins after March 6—and it will continue.
Sources: heise.de, tuvsud.com